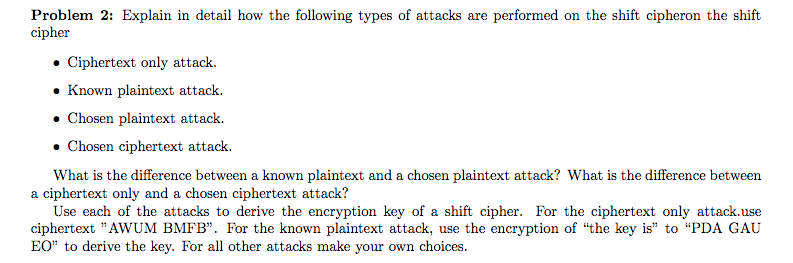
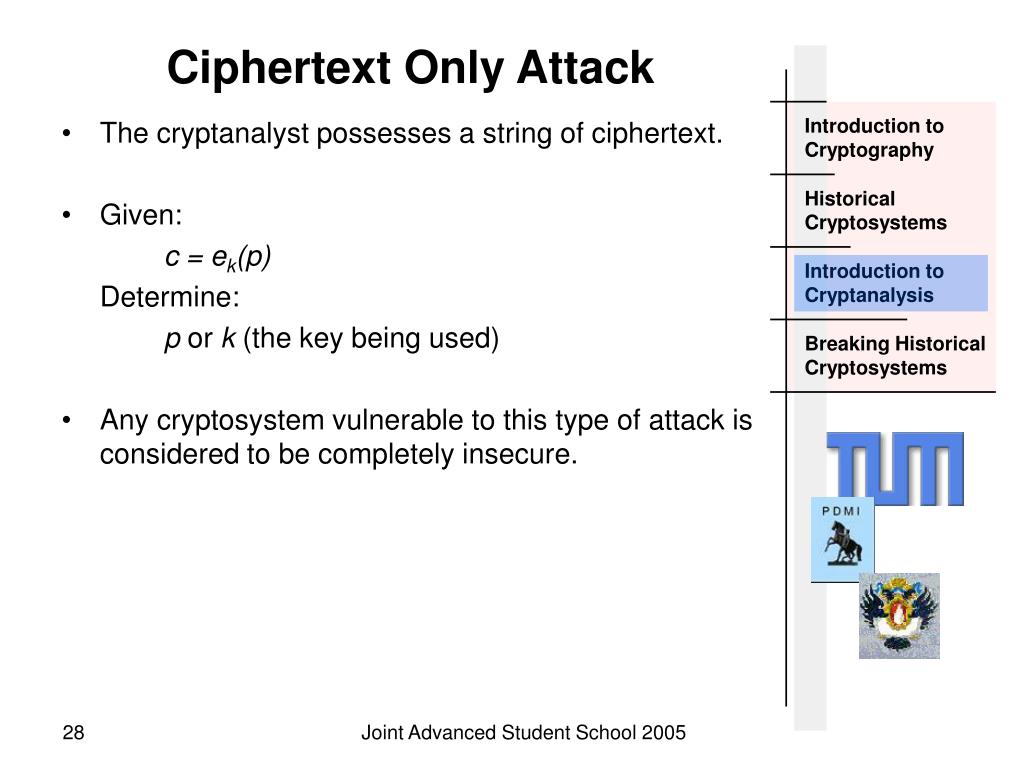
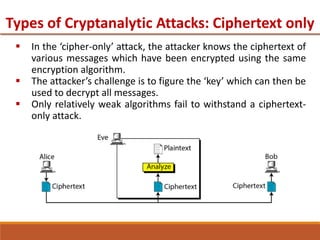
Ciphertext-only attack (COA) on the AE DRPE system: known ciphertext... | Download Scientific Diagram
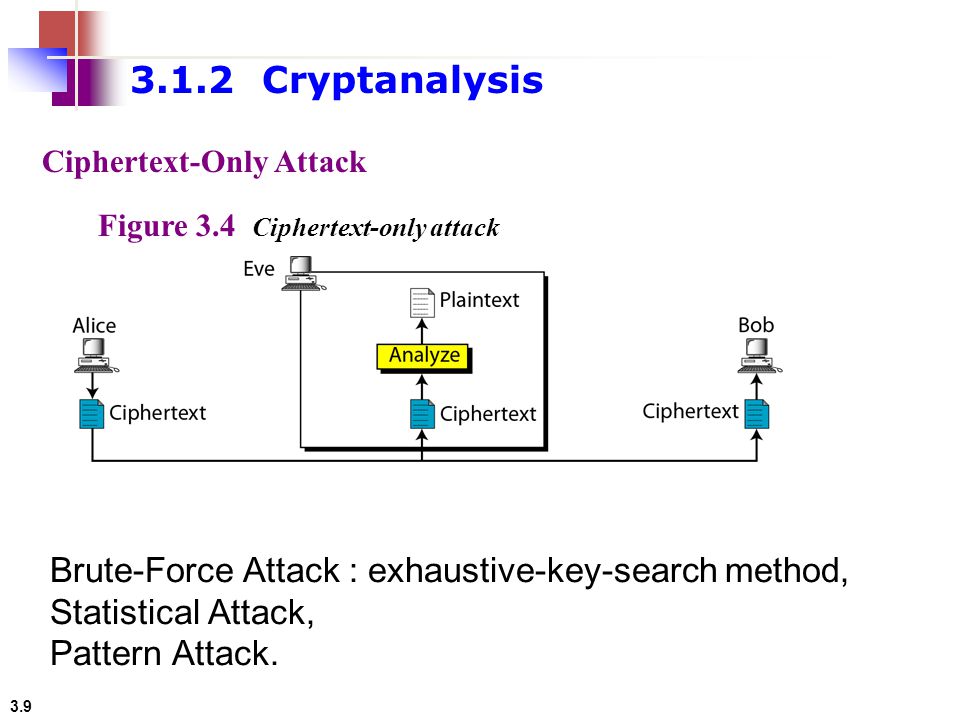
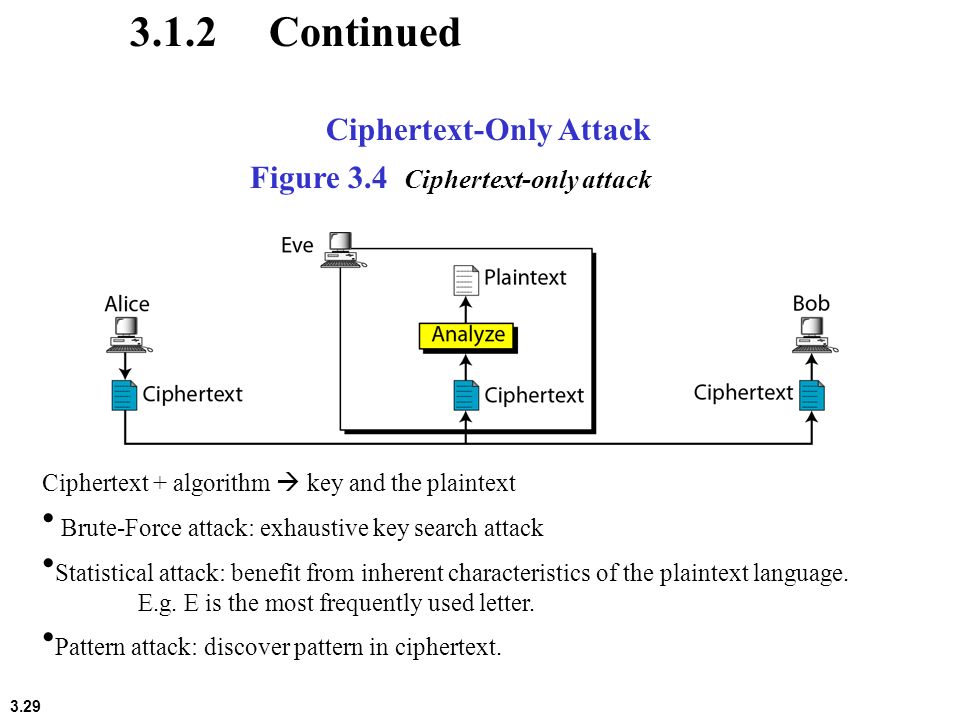
3.1 Copyright © The McGraw-Hill Companies, Inc. Permission required for reproduction or display. Chapter 3 Traditional Symmetric-Key Ciphers. - ppt download
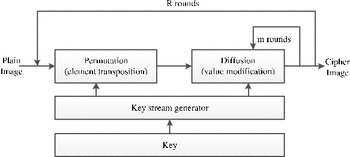
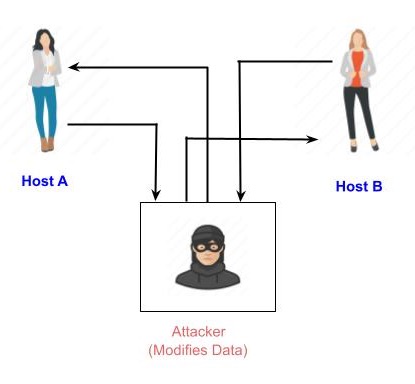
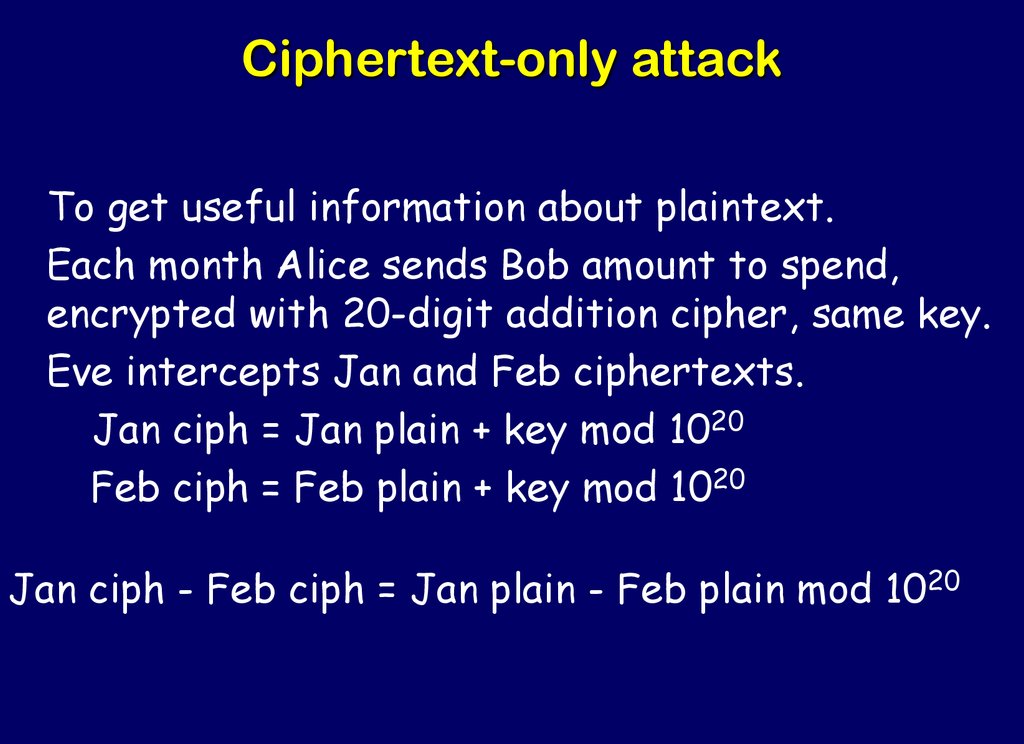
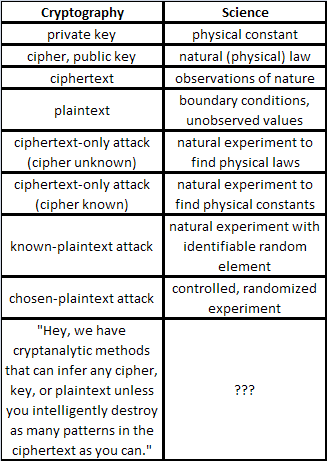
Basic Concepts in secure communication ❑ The security of the communication depends on the security of the key. It must be conv